I2P Router Help
Na jakich systemach I2P będzie działać?
I2P jest napisane w języku programowania Java. Oprogramowanie zostało przetestowane na systemach Windows, Linux, FreeBSD i macOS. Dostępny jest również port na Androida.
Odnośnie użycia pamięci: I2P jest domyślnie skonfigurowane do korzystania z 128 MB pamięci RAM. Jest to wystarczająco do przeglądania stron i IRC, ale inne aktywności mogą wymagać większej ilości pamięci. Do trasowania większych ilości danych, korzystania z BitTorrenta i hostowania intensywnie wykorzystywanych ukrytych usług, niezbędna jest większa ilość pamięci.
Odnośnie zużycia procesora: działanie I2P zostało sprawdzone na leciwych systemach, takich jak komputery jednopłytkowe Raspberry Pi. Ponieważ I2P korzysta z zaawansowanej kryptografii, mocniejszy procesor byłby odpowiedniejszy do korzystania z systemu obciążonego I2P i reszty zadań (usługi systemu operacyjnego, powłoka, inne procesy, przeglądarka internetowa).
Porównanie kilku dostępnych środowisk uruchomieniowych Javy (JRE) dostępne jest pod adresem: https://trac.i2p2.de/wiki/java. Zaleca się korzystanie z Javy od Sun/Oracle lub z OpenJDK.
Czy instalacja Javy jest wymagana aby korzystać z I2P?
Podczas gdy główna implementacja klienta I2P wymaga Javy, istnieje kilka alternatywnych klientów, które jej nie wymagają.
Czym jest strona .i2p?
Strona w domenie .i2p jest anonimowo hostowaną stroną internetową, ukrytą usługą dostępną poprzez przeglądarkę internetową. Można na nią wejść uprzednio konfigurując proxy swojej przeglądarki (zwykle na localhost i port 4444). Szczegółowe instrukcje znajdują się na stronie konfiguracji przeglądarki.
Co oznacza pole „aktywni: X/Y” w konsoli węzła?
X oznacza liczbę uczestników do których wysłałeś lub otrzymałeś wiadomość w przeciągu ostatniej minuty, Y oznacza liczbę uczestników z którymi kontaktowałeś się w ciągu ostatniej godziny. Najedź kursorem nad inne elementy, aby wyświetlić ich krótki opis.
Mam uprzedzenia do pewnych treści. Jak mogę się ustrzec przed rozsyłaniem, przechowywaniem i oglądaniem ich?
I2P traffic that transits through your router is encrypted with several layers of encryption. Except in the case of a serious security vulnerability (of which none are currently known), it is not possible to know the content, origin or destination of routed traffic.
-
Distribution
All traffic on the I2P network is encrypted in multiple layers. You don't know a message's contents, source, or destination. Traffic is internal to the I2P network, you are not an exit node (referred to as an outproxy in our documentation). -
Storage
The I2P network does not do distributed storage of content, this has to be specifically installed and configured by the user (with Tahoe-LAFS, for example). That is a feature of a different anonymous network, Freenet. By running an I2P router, you are not storing content for anyone. -
Access
Your router will not request any content without your specific instruction to do so.
Is it possible to block I2P?
Tak, najprostszą i najbardziej powszechną metodą jest zablokowanie serwerów pozwalających znaleźć nowe węzły – tzw. «reseed». Całkowite zablokowanie całego szyfrowanego ruchu również działałoby (jednakże spowodowałoby to zablokowane wielu usług niezwiązanych z I2P). W przypadku zablokowania serwerów reseed, wciąż można byłoby pobrać paczkę reseed z GitHuba, którą można byłoby zablokować blokując całkowicie dostęp do GitHuba. Wciąż możliwe byłoby przeprowadzić reseedowanie przez serwer proxy (oprócz sieci Tor jest wiele innych serwerów dostępnych na sieci), bądź pobranie (lub wymiana offline) paczki reseed od znajomego.
W plikuwrapper.log pojawia się błąd: „Protocol family unavailable” podczas ładowania konsoli węzła.
Ten błąd często występuje z programami Java wykorzystujących sieć na niektórych systemach skonfigurowanych do używania domyślnie IPv6. Jest na to kilka sposobów:
- Na systemach linuksowych, wpisz code>echo 0 > /proc/sys/net/ipv6/bindv6only
- Poszukaj następujących linii w
wrapper.config:
#wrapper.java.additional.5=-Djava.net.preferIPv4Stack=true
#wrapper.java.additional.6=-Djava.net.preferIPv6Addresses=false
Jeżeli je napotkasz, od-komentuj je poprzez usunięcie znaków „#”. Jeżeli ich nie ma, to je dodaj bez znaków „#”.
~/.i2p/clients.config.
UWAGA: wszelkie zmiany w wrapper.config wymagają całkowitego restartu węzła i wrappera. Samo kliknięcie Restart w konsoli węzła NIE przeładuje tego pliku! Musisz kliknąć Zamknij, poczekać 11 minut, i ponownie włączyć I2P.
Czy większość stron .i2p w sieci I2P jest martwa?
Jeżeli weźmiemy pod uwagę wszystkie strony .i2p w historii, to tak, większość z nich jest martwych. Ludzie i strony I2P rodzą się i odchodzą. Dobrym sposobem na rozpoczęcie przygody z I2P jest spojrzenie na listę czynnych stron .i2p. Strona http://identiguy.i2p.xyz śledzi aktywne strony I2P.
Dlaczego I2P nasłuchuje na porcie 32000?
Usługa wrappera Javy „Tanuki” otwiera ten port – przypięty pod localhost – aby komunikować się z oprogramowaniem uruchomionym wewnątrz JVM. Kiedy maszyna wirtualna Javy jest uruchamiana, tworzony jest klucz, potrzebny do połączenia z wrapperem. Po tym jak JVM utworzy połączenie z wrapperem, wrapper odrzuca wszystkie następne połączenia.
Więcej informacji jest dostępnych w dokumentacji wrappera.
Configuration
Jak mam skonfigurować przeglądarkę?
Instrukcje konfiguracji serwerów proxy dla różnych przeglądarek internetowych wraz z zrzutami ekranu znajdują się na osobnej stronie. Bardziej zaawansowane konfiguracje z użyciem narzędzi zewnętrznych takich jak rozszerzenie do przeglądarek FoxyProxy bądź serwer Privoxy są możliwe, ale ich niepoprawna konfiguracja grozi wyciekiem Twoich danych.
Jak mam się połączyć do IRC na I2P?
Tunel do głównego serwera IRC w sieci I2P – Irc2P – został utworzony podczas instalacji I2P (zajrzyj na stronę zarządzania ukrytymi usługami) i jest automatycznie uruchamiany podczas startu węzła. Aby się z nim połączyć, skonfiguruj swojego klienta IRC do łączenia się z serwerem localhost 6668. Użytkownicy programu HexChat mogą utworzyć nową sieć z serwerem localhost/6668 (zaznacz „pomiń serwer proxy”, jeżeli masz skonfigurowany serwer proxy). Użytkownicy programu Weechat mogą wpisać następujące polecenie:
/server add irc2p localhost/6668
Jak założyć własną stronę w sieci I2P?
Kliknij w odnośnik „serwer www” w konsoli Twojego węzła, aby dowiedzieć się więcej.
Czy hostowanie na komputerze w domu strony .i2p napisaną tylko w HTML i CSS jest niebezpieczne?
Jeżeli prowadzisz własny blog lub udostępniasz jakieś mało wrażliwe treści, to raczej nie jesteś w większym niebezpieczeństwie. Jeżeli potrzebujesz podstawowej prywatności, również nie jesteś w większym niebezpieczeństwie. Jeżeli hostujesz jakieś wrażliwe treści, Twoja usługa przestanie działać w tym samym momencie co Twój węzeł. Ktoś monitorujący czas niedostępności Twojej usługi może skorelować to z wydarzeniami w świecie rzeczywistym i zdeanonimizować Cię przy pewnych nakładach pracy. Można się przed tym bronić hostując usługę na wielu serwerach (multihoming) bądź korzystając z Tahoe-LAFS, ale wymaga do dodatkowej konfiguracji i jest odpowiednie tylko dla pewnego rodzaju zagrożeń. Nie istnieje jedno idealne rozwiązanie, ochrona przed inwigilacją wymaga rozważnych decyzji w każdym przypadku.
W jaki sposób węzeł odnajduje strony .i2p?
The I2P Address Book application maps human-readable names to long-term destinations, associated with services, making it more like a hosts file or a contact list than a network database or a DNS service. It's also local-first there is no recognized global namespace, you decide what any given .i2p domain maps to in the end. The middle-ground is something called a "Jump Service" which provides a human-readable name by redirecting you to a page where you will be asked "Do you give the I2P router permission to call $SITE_CRYPTO_KEY the name $SITE_NAME.i2p" or something to that effect. Once it's in your address book, you can generate your own jump URL's to help share the site with others.
Jak można dodać adresy do książki adresowej?
Nie można dodać adresu bez znajomości przynajmniej adresu Base32 lub Base64 strony. Łatwo zapamiętywalna nazwa hosta jest tylko aliasem adresu kryptograficznego, który odpowiada adresowi Base32/Base64. Bez tego adresu kryptograficznego nie ma możliwości odwiedzenia danej strony w sieci I2P. Rozpowszechnianiem adresów osobom, które jaszcze ich nie znają zajmują się „usługi skoków”. Przy wejściu na nieznany adres węzeł I2P zaproponuje użycia usługi skoków, z których stats.i2p jest najbardziej godną zaufania.
Hostowanie strony korzystając z wbudowanej aplikacji „i2ptunnel” nie spowoduje automatycznej rejestracji strony w usłudze skoków. Aby przydzielić nazwę lokalnie, wejdź na stronę konfiguracji i kliknij „dodaj do lokalnej książki adresowej”. Następnie przejdź do http://127.0.0.1:7657/dns i udostępnij innym odnośnik pomocniczy.
Jakich portów używa I2P?
Porty wykorzystywane przez I2P można umieścić w 2 kategoriach:
- Porty wystawione do internetu, używane do komunikacji z innymi węzłami I2P
- Porty lokalne, do połączeń lokalnych na Twoim systemie
Poniżej szczegółowy opis.
- Porty wystawione do internetu
Uwaga: od wersji 0.7.8 nowe instalacje nie wykorzystują portu 8887, tylko losowy port z przedziału [9000, 31000] wybrany podczas pierwszego uruchomienia węzła. Wybrany port jest wyświetlany na stronie konfiguracji węzła.
WYCHODZĄCE- UDP losowego portu wyświetlanego na stronie konfiguracji do dowolnych zdalnych portów UDP, z możliwością odpowiedzi
- losowy wysoki TCP do dowolnych zdalnych portów TCP
- UDP do portu 123, z możliwością odpowiedzi (jest to niezbędne do wewnętrznej usługi synchronizacji czasu I2P poprzez SNTP – odpytuje losowy serwer SNTP z pool.ntp.org lub inny wybrany przez użytkownika)
- (opcjonalny, zalecany) UDP wyświetlany na stronie konfiguracji z dowolnych zdalnych adresów
- (opcjonalny, zalecany) TCP wyświetlany na stronie konfiguracji z dowolnych zdalnych adresów
- przychodzący TCP można dezaktywować na stronie konfiguracji
- Lokalne porty I2P, nasłuchujące domyślnie tylko lokalnych połączeń, o ile nie zanotowano inaczej:
PORT WYKORZYSTANIE OPIS 1900 UPnP SSDP UDP multicast listener Niezmienialny. Podpina się pod wszystkie interfejsy. Może zostać wyłączony na stronie konfiguracji „sieć”. 2827 BOB bridge Gniazdo wysokopoziomowego API dla aplikacji klienckich. Domyślnie wyłączone. Może zostać włączony/wyłączony na stronie konfiguracji „klienty”. Można zmienić w pliku bob.config. 4444 HTTP proxy Może zostać wyłączony lub zmieniony na stronie „zarządzanie ukrytymi usługami” w konsoli węzła. Można również przypiąć do określonego lub wszystkich interfejsów sieciowych. 4445 HTTPS proxy Może zostać wyłączony lub zmieniony na stronie „zarządzanie ukrytymi usługami” w konsoli węzła. Można również przypiąć do określonego lub wszystkich interfejsów sieciowych. 6668 IRC proxy Może zostać wyłączony lub zmieniony na stronie „zarządzanie ukrytymi usługami” w konsoli węzła. Można również przypiąć do określonego lub wszystkich interfejsów sieciowych. 7652 HTTP TCP event listener Podpina się pod adresy LAN. Może zostać zmieniony używając zaawansowanego ustawienia i2np.upnp.HTTPPort=nnnn. Może zostać wyłączony na stronie konfiguracji „sieć”.7653 UPnP SSDP UDP search response listener Podpina się pod adresy LAN. Może zostać zmieniony używając zaawansowanego ustawienia i2np.upnp.SSDPPort=nnnn. Może zostać wyłączony na stronie konfiguracji „sieć”.7654 I2P Client Protocol port Używane przez aplikacje klienckie. Można zmienić port na stronie konfiguracji „klienty”, ale nie jest to zalecane. Można podpiąć do określonego lub wszystkich interfejsów sieciowych, lub zostać wyłączony. 7655 UDP for SAM bridge Gniazdo wysokopoziomowego API dla aplikacji klienckich. Otwierany tylko gdy klient SAM v3 zażąda sesji UDP. Może zostać włączony/wyłączony na stronie konfiguracji „klienty”. Może zostać zmieniony w pliku clients.configw linijcesam.udp.port=nnnn.7656 SAM bridge Gniazdo wysokopoziomowego API dla aplikacji klienckich. Domyślnie wyłączony dla świeżych instalacji od wersji 0.6.5. Może zostać włączony/wyłączony na stronie konfiguracji „klienty”. Może zostać zmieniony w pliku clients.config.7657 Your router console Może zostać wyłączony w pliku clients.config. Może również zostać przypisany do określonego lub wszystkich interfejsów sieciowych w tym pliku konfiguracyjnym.7658 Your I2P Site Może zostać wyłączony w pliku clients.config. Może również zostać przypisany do określonego lub wszystkich interfejsów sieciowych w plikujetty.xml.7659 Outgoing mail to smtp.postman.i2p Może zostać wyłączony lub zmieniony na stronie „zarządzanie ukrytymi usługami” w konsoli węzła. Można również przypiąć do określonego lub wszystkich interfejsów sieciowych. 7660 Incoming mail from pop3.postman.i2p Może zostać wyłączony lub zmieniony na stronie „zarządzanie ukrytymi usługami” w konsoli węzła. Można również przypiąć do określonego lub wszystkich interfejsów sieciowych. 7670 (8998) gitssh.idk.i2p git over ssh This used to be port 8998 for monotone. Elder installations may still have that and not this one. May be disabled or changed on the i2ptunnel page in the router console. May also be configured to be bound to a specific interface or all interfaces. 31000 Local connection to the wrapper control channel port Wychodzący tylko na 32000, nie nasłuchuje na tym porcie. Rozpoczyna od 31000 i kolejno szuka wolnego portu aż do 31999. Aby zmienić, zajrzyj do dokumentacji wrappera. Więcej informacji poniżej. 32000 Local control channel for the service wrapper Aby zmienić, zajrzyj do dokumentacji wrappera. Więcej informacji poniżej.
Lokalne porty i porty tuneli ukrytych usług I2P nie muszą być osiągalne ze zdalnych maszyn, ale powinny być osiągalne lokalnie. Możesz także potrzebować dodatkowych portów dla utworzonych tuneli ukrytych usług I2P na stronie „zarządzanie ukrytymi usługami ”(które też wymagałyby lokalnego dostępu, ale nie zdalnego, o ile tego nie potrzebujesz).
Podsumowując, żadne porty nie muszą być dostępne z zewnątrz, ale jeżeli potrafisz skonfigurować swój NAT/zaporę sieciową, aby przekierować przychodzące połączenia UDP i TCP do portu skonfigurowanego na tej stronie, będziesz się cieszył(a) większą wydajnością. Musisz też zezwolić na wychodzące pakiety UDP do dowolnych zdalnych komputerów (blokowanie losowych IP narzędziami typu PeerGuardian tylko przynosi więcej szkody niż pożytku – nie rób tego).
Brakuje mnóstwa adresów w mojej książce adresowej. Gdzie są jakieś dobre linki do subskrypcji?
Odpowiedź na to pytanie składa się z 3 części:
- Mój węzeł często wyświetla komunikat „nie znaleziono strony www w książce adresowej”, jaka jest tego przyczyna?
Czytelne dla ludzi adresy, takie jak http://website.i2p są odnośnikami do długich ciągów znaków określanych jako miejsca przeznaczenia. Te odnośniki są rejestrowane i przetrzymywane w usługach książek adresowych takich jak np. stats.i2p (zarządzana przez użytkownika zzz). Często spotkasz się z adresami „b32”. Adres „b32” jest zahaszowanym (dokładnie przez funkcję SHA256) adresem miejsca przeznaczenia. Do tego haszu jest doklejony ciąg „.b32.i2p”, aby utworzyć klikalny odnośnik do ukrytej usługi, który nie wymaga rejestracji w książce adresowej.
Można dodać zasubskrybować adresy do książki adresowej Twojego węzła, aby komunikat ten pojawiał się rzadziej.
- Czym jest subskrypcja książki adresowej?
Są to pliki hostowane na różnych witrynach w sieci I2P zawierające listy stron .i2p wraz z odpowiadającymi im przeznaczeniami.
Książka adresowa znajduje się w konsoli węzła pod adresem http://localhost:7657/dns, gdzie znajdują się dalsze informacje.
- Gdzie znajdę jakieś dobre subskrypcje książki adresowej?
Skorzystaj z następujących:
Jak mogę dostać się do konsoli węzła z innych komputerów lub zablokować dostęp hasłem?
Ze względów bezpieczeństwa, konsola administracyjna węzła domyślnie nasłuchuje połączeń tylko na lokalnym interfejsie sieciowym. Są dwie metody na zdalny dostęp do konsoli węzła:
- Tunel SSH
- Konfiguracja konsoli. aby była dostępna z zewnątrz z publicznego adresu IP i chroniona hasłem
Opisy poniżej:
- Tunel SSH
Na systemach uniksopodobnych, jest to najłatwiejszy sposób na zdalny dostęp do konsoli węzła I2P.
(Uwaga: serwer SSH jest również dostępny na system Windows, na przykład https://github.com/PowerShell/Win32-OpenSSH.)
Po skonfigurowaniu dostępu do Twojego systemu przez SSH, użyj parametru „-L” z odpowiednimi argumentami, przykład:ssh -L 7657:localhost:7657 (System_IP)ssh -NL 7657:localhost:7657 (System_IP) - Konfiguracja konsoli. aby była dostępna z zewnątrz z publicznego adresu IP i chroniona hasłem
- Otwórz plik
~/.i2p/clients.configi zastąpclientApp.0.args=7657 ::1,127.0.0.1 ./webapps/clientApp.0.args=7657 ::1,127.0.0.1,(System_IP) ./webapps/ - Przejdź do http://localhost:7657/configui i opcjonalnie zabezpiecz swoją konsolę węzła I2P nazwą użytkownika i hasłem – jest to szczególnie zalecane, aby ktoś nie namieszał w Twojej konsoli narażając Cię na demaskację.
- Przejdź do http://localhost:7657/index i kliknij „restart”, aby zrestartować JVM i przeładować aplikacje klienckie.
http://(publiczny adres IP):7657i wpisz uprzednio zdefiniowaną nazwę użytkownika i hasło, jeżeli Twoja przeglądarka obsługuje okienko uwierzytelniania.
Uwaga: możesz wpisać w powyższej konfiguracji 0.0.0.0. Jest to określenie interfejsu sieciowego, nie sieci lub maski podsieci. 0.0.0.0 oznacza podpięcie się pod wszystkie interfejsy sieciowe, więc będzie osiągalne zarówno z 127.0.0.1:7657, z sieci lokalnej (LAN) i z internetu (WAN). Bądź ostrożny/a korzystając z tej opcji, ponieważ konsola będzie wtedy dostępna ze WSZYSTKICH adresów skonfigurowanych w systemie. - Otwórz plik
Jak mogę używać aplikacji z moich innych komputerów?
Przeczytaj odpowiedź na poprzednie pytanie odnośnie instrukcji przekierowania portów przez SSH, zajrzyj również na stronę w konsoli węzła: http://localhost:7657/configi2cp.
Czy jest możliwe użycie I2P jako proxy SOCKS?
Proxy SOCKS działa od wydania 0.7.1. Wspierane są SOCKS 4/4a/5. I2P nie ma proxy wyjściowego SOCKS, więc będzie to użyteczne tylko do przeglądania domen .i2p.
Wiele aplikacji może powodować wyciek wrażliwych danych, które mogą Cię zdemaskować, więc zaleca się ostrożność podczas korzystania przez I2P z proxy SOCKS. I2P anonimizuje tylko informacje o połączeniu, ale jeżeli jakaś aplikacja przesyła te informacje w zawartości, oprogramowanie I2P nie ma możliwości chronić Twojej prywatności. Przykład: niektóre klienty pocztowe przesyłają adres IP systemu na którym pracują na serwera pocztowego. I2P nie ma możliwości odfiltrować tych informacji, więc używanie I2P jako proxy SOCKS dla aplikacji jest możliwe, ale niezwykle niebezpieczne.
W każdym bądź razie, jeżeli chcesz więcej informacji o proxy SOCKS, kilka użytecznych wskazówek znajdziesz na tej stronie.
Jak mogę połączyć się z IRC, BitTorrentem, lub innymi usługami w normalnym Internecie?
O ile została założona usługa proxy wyjściowego do usługi z którą się chcesz połączyć, nie jest to możliwe. Obecnie są tylko trzy typy proxy wyjściowego w sieci I2P: HTTP, HTTPS, e-poczta. Nie ma obecnie proxy wyjściowego SOCKS. Jeżeli potrzebujesz z tego typu usługi, zainteresuj się siecią Tor. Proszę mieć na uwadze fakt, że programiści projektu Tor odradzają korzystanie z BitTorrenta poprzez Tor z powodu poważnych problemów z bezpieczeństwem wynikających z takiego postępowania.
Privacy and Safety
Czy mój węzeł jest „węzłem wyjściowym” do normalnego Internetu? Nie chcę aby nim był.
Nie. W przeciwieństwie do sieci Tor „węzły wyjściowe” (a dokładniej „outproxy” w terminologii I2P) nie są niezbędną częścią sieci. Tylko wolontariusze, którzy skonfigurowali specjalne oprogramowanie tworzą bramki do zwykłego internetu. Jest ich dosłownie kilku. Domyślnie proxy wyjściowe HTTP (skonfigurowane na porcie 4444) zawiera tylko jeden taki serwer: false.i2p. Jeżeli ciekawi Cię jak uruchomić własne proxy wyjściowe, na forum I2P znajduje się poradnik (en).
Czy korzystanie z I2P jest bezpieczne?
Before you use I2P, use Basic Computer Hygiene Always! Apply your OS vendor provided software updates in a prompt manner. Be aware of the state of your firewall and anti-virus status if you use one. Always get your software from authentic sources.
I2P usiłuje być bezpieczne w domyślnej konfiguracji dla większości użytkowników.
Może być niebezpieczne korzystanie z sieci I2P w tak zwanych „opresyjnych państwach”, gdzie prawo może zabraniać korzystania z oprogramowania anonimizującego. Większość użytkowników I2P nie znajduje się w takich państwach, a węzły użytkowników w opresyjnych państwach przechodzą w „tryb ukryty”, w którym interakcje z resztą sieci są ograniczone, aby byli mniej widoczni dla obserwujących sieć.
Widzę adresy IP innych użytkowników sieci I2P w konsoli węzła. Czy to oznacza, że mój adres IP jest widoczny dla innych?
Tak, w ten sposób działa w pełni rozproszona sieć P2P. Każdy uczestniczy w przesyłaniu pakietów innych użytkowników, więc Twój adres IP musi być znany innym, aby nawiązywać połączenia.
Pomimo tego, że fakt korzystania przez Ciebie z sieci I2P jest jawny, inni nie mają wglądu co do tego co robisz w sieci I2P. Nie można stwierdzić, czy dany użytkownik sieci I2P dzieli się plikami, hostuje stronę, przegląda, czy tylko pośredniczy w ruchu innych użytkowników.
Jak łatwo można wykryć korzystanie z I2P analizując ruch sieciowy?
Można z pewnym prawdopodobieństwem wywnioskować czy ktoś korzysta z sieci I2P, ale ciężko być tego pewnym. Najpewniejszym sposobem byłoby znajomość adresu IP (o ile jest stały) komputera podejrzanego, a następnie posiadanie kilku monitorowanych węzłów sieci I2P w różnych sieciach. Kiedy jeden z nich połączy się z podejrzanym komputerem, jego węzeł I2P pojawi się w bazie węzłów. Może to zająć trochę czasu, a może wcale nie nastąpić. Możesz również całkowicie blokować szyfrowany ruch w określonej sieci, aby każdy węzeł I2P z tej sieci stracił wszystkich użytkowników. W tym momencie węzły te połączą się z serwerami reseedowania, co administrator sieci powinien z łatwością zaobserwować.
Czy używanie proxy wyjściowego (outproxy) jest bezpieczne?
I2P nie szyfruje transferu w internecie, sieć Tor także nie, np. korzystając z protokołu TLS. Celem obydwu sieci jest przesłanie danych w postaci niezmienionej i anonimowo przez sieć do odbiorcy. Każdy nieszyfrowany ruch sieciowy generowany na Twoim systemie trafi w końcu do proxy/węzła wyjściowego jako nieszyfrowany. Oznacza to, że Twój ruch sieciowy może być przechwycony przez operatorów proxy/węzłów wyjściowych. Sposobem na ochronę ruchu przed tym zagrożeniem jest upewnienie się, że cały ruch do proxy wyjściowego będzie szyfrowany przez TLS.
Więcej informacji znajdziesz na stronie projektu Tor: https://www.torproject.org/docs/faq#CanExitNodesEavesdrop (w j. angielskim).
Ponadto, możesz być zagrożony na skutek zmowy pomiędzy operatorem proxy wyjściowego i innych usług w I2P, jeśli używasz tych samych tuneli (opcja „klient współdzielony)”. Dyskusja na ten temat została przeprowadzona na zzz.i2p. Wykonano również kopię tej dyskusji na modelu zagrożenia i zaufania do operatora proxy wyjściowego.
Co z atakami deanonimizującymi?
Zmniejszenie anonimowości może nastąpić na skutek:
A) identyfikacji cech spójnych anonimowych tożsamości
B) identyfikacji cech ulotnych powtarzanych połączeń.
Mówimy tylko o zmniejszeniu anonimowości, ponieważ wiele z tych cech jest wspólnych dla wielu użytkowników tworzących „zbiór”. W im mniejszym zbiorze się znajdujesz i w jak wielu małych zbiorach się znajdujesz, tym mniejsza jest Twoja anonimowość.
W przeszłości ataki na sieć I2P polegały na korelacji bazy dany sieci i weryfikacji. Dodając element losowości pomiędzy bazą danych i weryfikacją zmniejszono prawdopodobieństwo powiązania z aktywnością w sieci I2P, zmniejszając tym samym skuteczność tego ataku.
Ataki na oprogramowanie skonfigurowane do pracy z siecią I2P są poza zakresem możliwości zespołu I2P. Użytkownik przeglądający strony .i2p bądź hostujący własną stronę w sieci I2P musi samodzielnie przemyśleć model zagrożenia. Przeglądarki internetowe są szczególnie problematyczne, ponieważ zostawiają „odcisk palca przeglądarki”. Korzystanie ze zestandaryzowanego profilu przeglądarki pozwala zmniejszyć to ryzyko.
Reseeds
Mój węzeł jest aktywny od kilku minut i nawiązał zero lub bardzo mało połączeń
Nowe instalacje I2P przeprowadzają proces reseedowania automatycznie kiedy liczba znanych uczestników spadnie do bardzo niskiej wartości. Jeżeli potrzebujesz ręcznie przeprowadzić reseedowanie swojego węzła, zajrzyj do instrukcji reseedowania.
Jak przeprowadzić ręczny reseed?
Węzeł I2P musi zostać reseedowany podczas pierwszego połączenia z siecią. Reseedowanie polega na pobraniu kilku plików zawierających informacje o węzłach (zapakowanych w cyfrowo podpisany plik .zip) po HTTPS z co najmniej dwóch predefiniowanych serwerów prowadzonych przez wolontariuszy w zwykłym internecie.
Typowym objawem nieudanego reseedowania jest wskaźnik „znani” (po lewej stronie konsoli węzła) wyświetlający bardzo małą wartość (często mnij niż 5), która nie rośnie. To może się zdarzyć, między innymi gdy Twoja zapora sieciowa blokuje ruch wychodzący lub żądanie reseedowania jest całkowicie zablokowane.
Jeżeli utknąłeś za zaporą Twojego dostawcy internetu lub jakiegoś filtra, możesz ręcznie połączyć się z siecią I2P.
Wraz z wydaniem 0.9.33 możesz także skonfigurować swój węzeł, aby reseedował przez proxy. Przejdź do http://localhost:7657/configreseed i skonfiguruj rodzaj proxy, nazwę hosta i port.
Dołączanie do sieci I2P za pomocą pliku reseed
Skontaktuj się z zaufanym kolegą posiadającym węzeł I2P i poproś go o pomoc w reseedowaniu Twojego węzła I2P. Poproś go o przesłanie pliku reseed wyeksportowanego z jego węzła I2P. Jest ważne, aby ten plik został przesłany bezpiecznym kanałem, np. w postaci zaszyfrowanej (PGP, podpisz, zaszyfruj i zweryfikuj zaufanym kluczem publicznym), aby nie został przez kogoś zmodyfikowany. Plik ten jest niepodpisany, więc ufaj tylko plikom od zaufanych osób. Nigdy nie importuj pliku reseed z nieznanego źródła.
Aby zaimportować otrzymany plik i2preseed.zip do swojego węzła:
- przejdź na stronę http://localhost:7657/configreseed
- w sekcji „reseed z pliku” kliknij „przeglądaj…”
- wybierz plik i2preseed.zip
- kliknij „reseeduj z pliku”
Sprawdź, czy w dzienniku pojawił się wpis:
Reseed got 100 router infos from file with 0 errors
Udostępnianie pliku reseed
Zaufani znajomi mogą wykorzystać Twój węzeł I2P, aby podłączyć się do sieci:
- przejdź na stronę http://localhost:7657/configreseed
- przejdź do sekcji „utwórz plik reseedowania”
- bezpiecznie wyślij plik i2preseed.zip swojemu znajomemu
Nie udostępniaj tego pliku nieznajomym gdyż zawiera on wrażliwe informacje prywatne (100 informacji o węzłach) z Twojego węzła I2P! Aby chronić swoją anonimowość możesz poczekać kilka godzin/dni zanim udostępnisz ten plik przyjacielowi. Zaleca się oszczędnie korzystać z tej procedury (< 2 razy na tydzień).
Ogólne wytyczne dotyczące ręcznego reseedu I2P
- Nie udostępniaj publicznie lub znajomemu znajomego pliku reseed!
- Udostępniaj ten plik tylko ograniczonej liczbie osób (< 3)!
- Plik ten jest ważny tylko kilka dni (< 20)!
Internet Access/Performance
Nie mogę przeglądać normalnych stron internetowych przez I2P.
Sieć I2P nie została zaprojektowana do bycia bramką do zwykłego internetu. Jak już wspomniano, istnieją usługi – uruchamiane przez wolontariuszy – umożliwiające dostęp do zwykłego internetu, tak zwane „outproxy”. Jest jedno proxy wyjściowe domyślnie skonfigurowane w tunelu klienckim HTTP: false.i2p. Usługa ta obecnie działa, ale nie gwarantujemy, że będzie zawsze działała, ponieważ nie jest to oficjalna usługa dostarczana przez projekt I2P. Jeżeli Twoim głównym celem jest dostęp do treści w zwykłym nieanonimowym internecie, zalecamy skorzystanie z projektu Tor.
Nie mogę połączyć się z stronami https:// lub ftp:// przez I2P.
- HTTPS
Wewnątrz sieci I2P nie ma potrzeby korzystania z HTTPS. Wszystkie transfery są szyfrowane od-końca-do-końca, każda dodatkowa warstwa szyfrowania (np. HTTPS) nie zwiększa anonimowości. Jednakże jeżeli ktoś chciałby/musi skorzystać z HTTPS, domyślne proxy HTTP wspiera ruch HTTPS. Operator ukrytej usługi musiałby specjalnie skonfigurować i aktywować dostęp po HTTPS. - FTP
FTP nie jest wspierane z powodów technicznych. Obecnie nie ma proxy wyjściowych FTP, być może nawet nie dałoby się utworzyć takiej usługi. Każdy inny rodzaj proxy wyjściowego powinno się dać utworzyć wybierając opcję tunelu „standardowy”. Jeżeli chciał(a)byś założyć własne outproxy, ostrożnie zapoznaj się z potencjalnymi zagrożeniami. Społeczność I2P być może będzie w stanie udzielić Ci porad technicznych, nie bój się pytać. Jak już wcześniej wspomniano, każda usługa proxy wyjściowego nie jest podstawową usługą sieci I2P. Są to usługi uruchamiane przez wolontariuszy, mogą one zniknąć w każdej chwili.
Mój węzeł intensywnie korzysta z procesora, co można z tym zrobić?
Istnieje wiele różnych powodów wysokiego użycia procesora. Kolejno:
-
JRE
Spróbuj użyć albo OpenJDK albo Javy od Sun/Oracle jeżeli jest dostępna na Twój system. Możesz sprawdzić którą wersję Javy masz zainstalowaną wpisującjava -versiondo konsoli/powłoki. Na innych implementacjach Javy wydajność jest słaba. -
programy do wymiany plików, np. BitTorrent
Masz włączony klient BitTorrent przez I2P? Spróbuj zredukować liczbę torrentów, limity pobierania, lub wyłącz go całkowicie aby sprawdzić czy to coś pomoże. -
wysokie ustawienia przepustowości
Może Twoje limity przepustowości są zbyt wysokie? Być może zbyt dużo transferu jest przesyłane przez Twój węzeł I2P i jest on przeciążony. Spróbuj zmniejszyć procent udostępnianego pasma na stronie konfiguracji. -
wersja I2P
Upewnij się, że korzystasz z najnowszej wersji I2P aby czerpać korzyści z poprawek błędów i wydajnościowych. -
przydział pamięci
Czy wystarczająca ilość pamięci została zarezerwowana dla I2P? Spójrz na wykres pamięci na stronie wykresów i sprawdź, czy wykres nie jest „przycięty” – JVM spędza większość czasu na odśmiecaniu pamięci (ang. garbage collection). Zwiększ wartośćwrapper.java.maxmemoryw plikuwrapper.config. -
Bursts of high-usage vs. constant 100% usage
Czy użycie procesora jest po prostu wyższe nie byś chciał(a), czy cały czas wynosi 100%? Jeżeli stale wynosi 100% to może to być jakiś błąd. Zajrzyj do dziennika węzła po dalsze informacje. -
związane z Javą
Być może używasz opartej na Javie biblioteki BigInteger zamiast natywnej wersji, zwłaszcza jeżeli masz nowy lub nietypowy sprzęt lub system (OpenSolaris, mipsel, itp.). Zajrzyj na stronę jbigi po instrukcje na temat diagnozowania, kompilacji i metod testowania. -
tunele uczestniczące
Jeżeli Twoja natywna biblioteka jbigi działa poprawnie, największym pożeraczem CPU prawdopodobnie jest przekazywany ruch uczestniczących tuneli. To wykorzystuje CPU, ponieważ przy każdym skoku każda kolejna warstwa szyfrowania musi zostać zdekodowana. Możesz zmniejszyć ruch uczestniczący na dwa sposoby – poprzez redukcję udostępnianej przepustowości na stronie confignet.jsp lub poprzez ustawienie router.maxParticipatingTunnels=nnn na stronie configadvanced.jsp.
Mój węzeł ma bardzo mało aktywnych uczestników, czy to jest OK?
Jeżeli Twój węzeł łączy się z 10 lub więcej aktywnymi uczestnikami, to wszystko jest w porządku. Węzeł I2P przez cały czas powinien utrzymywać łączność z kilkoma uczestnikami. Najlepszym sposobem na bycie „lepiej połączonym” z siecią jest udostępnianie większej ilości pasma. Ilość pasma udostępnianego przez węzeł można skonfigurować na stronie http://localhost:7657/config.
Moi aktywni uczestnicy / znani uczestnicy / uczestniczące tunele / połączenia / przepustowość zmieniają się jak szalone z czasem! Czy jest coś nie tak?
Nie, to jest normalne zachowanie. Każdy węzeł dynamicznie dostosowuje się do zmieniających się warunków sieci i potrzeb. Węzły przyłączają i odłączają się od sieci w zależności od tego czy maszyny na których są zainstalowane są włączone/wyłączone i czy są połączone bądź odłączone od internetu. Twój węzeł na bieżąco aktualizuje swoją bazę danych sieci (NetDB). Tunele w których uczestniczy Twój węzeł wygasają po 10 minutach i mogą być odnowione przez Twój węzeł.
Dlaczego pobieranie plików, przeglądanie stron, ogółem wszystko jest wolniejsze w sieci I2P niż w normalnym internecie?
Szyfrowanie i trasowanie pakietów w sieci I2P stanowi znaczący narzut i zmniejsza dostępną przepustowość. Można to wyjaśnić za pomocą rysunku:
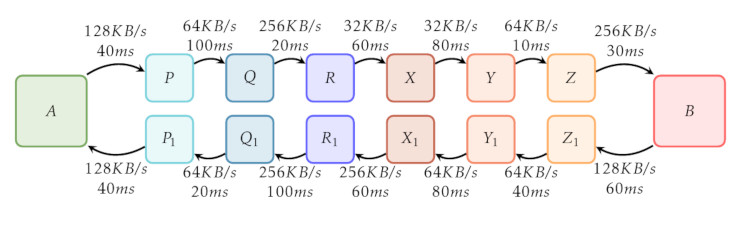
Na tym rysunku jest prześledzona droga wiadomości w sieci I2P. Węzeł użytkownika I2P jest oznaczony jako „A”, a ukryta usługa (przykładowo strona http://stats.i2p) jest oznaczony jako „B”. Zarówno klient jak i serwer korzystają z 3-skokowych tuneli, te skoki są reprezentowane jako: „P”, „Q”, „R”, „X”, „Y”, „Z”, „P₁”, „Q₁”, „R₁”, „X₁”, „Y₁” i „Z₁”.
„P”, „Q” i „R” reprezentują tunel wychodzący dla „A”; „X₁”, „Y₁” i „Z₁” reprezentują tunel wychodzący dla „B”. Analogicznie „X”, „Y” i „Z” reprezentują tunel przychodzący dla „B”, oraz „P₁”, „Q₁” i „R₁” oznaczają tunel przychodzący dla „A”. Strzałki symbolizują kierunek ruchu pakietów. Teksty nad i pod strzałkami symbolizują przepustowość i opóźnienie pomiędzy parami skoków.
Kiedy zarówno klient jak i serwer korzystają z 3‑skokowych tuneli, sumarycznie 12 innych węzłów sieci I2P tuneluje ruch. 6 uczestników pośredniczy w transferze od klienta do serwera, na transfer ten składa się 3‑skokowy tunel wychodzący z „A” („P”, „Q”, „R”) i 3‑skokowy tunel przychodzący do „B” („X”, „Y”, „Z”). W podobny sposób 6 uczestników pośredniczy w transferze od serwera do klienta.
Na początek rozważmy opóźnienie – czas potrzebny na wysłanie zapytania od klienta przez sieć I2P do serwera i wysłanie odpowiedzi z powrotem do klienta. Dodając opóźnienia otrzymujemy:
40 + 100 + 20 + 60 + 80 + 10 + 30 ms (client to server)
+ 60 + 40 + 80 + 60 + 100 + 20 + 40 ms (server to client)
-----------------------------------
TOTAL: 740 ms
W naszym przykładzie jest to 740 ms – zdecydowanie więcej niż podczas normalnego przeglądania internetu.
Teraz prześledźmy dostępną przepustowość. Jest ona zależna od najwolniejszego połączenia pomiędzy skokami od klienta do serwera, oraz także od serwera do klienta. Dostępna przepustowość dla ruchu wychodzącego od klienta do serwera w naszym przykładzie pomiędzy uczestnikami „R” i „X” oraz pomiędzy „X” i „Y” wynosi 32 KB/s. Pomimo większej dostępnej przepustowości pomiędzy innymi skokami, te skoki są wąskim gardłem i limitują maksymalną dostępną przepustowość od „A” do „B” na 32 KB/s. W podobny sposób można prześledzić trasę od serwera do klienta i wykazać, że dostępna przepustowość wynosi 64 KB/s – pomiędzy skokami „Z₁” i „Y₁” oraz „Y₁” i „X₁” oraz „Q₁” i „P₁”.
Zalecamy, abyś zwiększył(a) swoje limity przepustowości. Pomoże to sieci zwiększając dostępną przepustowość, co podniesie Twój komfort korzystania z sieci I2P. Ustawienia przepustowości są konfigurowalne na stronie http://localhost:7657/config. Proszę mieć na uwadze fakt, że limity połączenia internetowego zależą od dostawcy łącza internetowego.
Również zalecamy ustawienie wystarczającej ilości udostępnianego pasma – pozwala to na uczestnictwo w tunelowaniu ruchu innych uczestników przez Twój węzeł I2P. Tunelowanie ruchu innych sprawia, że Twój węzeł jest dobrze zintegrowany z siecią i zwiększa szybkości Twoich transferów.
I2P jest wciąż w fazie rozwoju. Jest wprowadzane mnóstwo ulepszeń i poprawek, i ogólnie mówiąc, korzystanie z najnowszej wersji ma pozytywny wpływ na wydajność. Jeżeli tego nie zrobiłeś, to zainstaluj najnowszą wersję.
Znalazłem błąd, gdzie go mogę zgłosić?
Napotkane błędy/problemy można zgłaszać na naszym systemie śledzenia błędów, dostępnym zarówno z normalnego internetu jak i z I2P. Mamy również forum – dostępne z I2P i z normalnego internetu. Mamy również kanał IRC – dostępny poprzez I2P (Irc2P) lub poprzez Freenode.
- System śledzenia błędów:
- zwykły internet: https://i2pgit.org/I2P_Developers/i2p.i2p/issues
- sieć I2P: http://git.idk.i2p/I2P_Developers/i2p.i2p/issues
- Forum: i2pforum.net
- Możesz wkleić powiązany dziennik zdarzeń do wklejarki (pastebin), listę wklejarek w zwykłym internecie znajdziesz na PrivateBin Wiki; w sieci I2P dostępny jest ten serwer PrivateBin bądź ten serwer niewymagający JavaScriptu, a następnie wejdź na kanał #i2p na naszym IRC./li>
- Porozmawiaj z programistami na IRC-u na kanale #i2p-dev
Prosimy zawrzeć powiązane informacje z dziennika zdarzeń węzła, który jest dostępny pod adresem http://127.0.0.1:7657/logs. Prosimy o udostępnienie całego tekstu z sekcji „wersja I2P i środowisko uruchomieniowe” wraz z błędami/ostrzeżeniami wyświetlanymi w dzienniku na stronie konsoli.
Mam pytanie!
Świetnie! Znajdziesz nasz na IRC:
- na kanale
#i2pnairc.freenode.net - na kanale
#i2pnaIRC2P


























